The CISSP is THE GOLD standard
of Cybersecurity certifications!

Getting your CISSP certification is a smart career move, it is:
-
Recognized The CISSP is widely recognized by recruiters and HR. It is seen as the GOLD standard of IT and Cybersecurity certifications.
Get Your Complete CISSP bundle now!
430,000+ Enrollments
4.7 Rating
Fully 2024 Exam updated
-
34 hours of CISSP videos Covering all 8 domains
Study and Exam Tips, Tricks, and Approaches -
5,000+ CISSP questions 625 Hard questions
750 Complex questions
3,250 Easy/Mid questions
- Both Exam mode and Per-Domain
201 Major Topic questions
240 End of Domain questions -
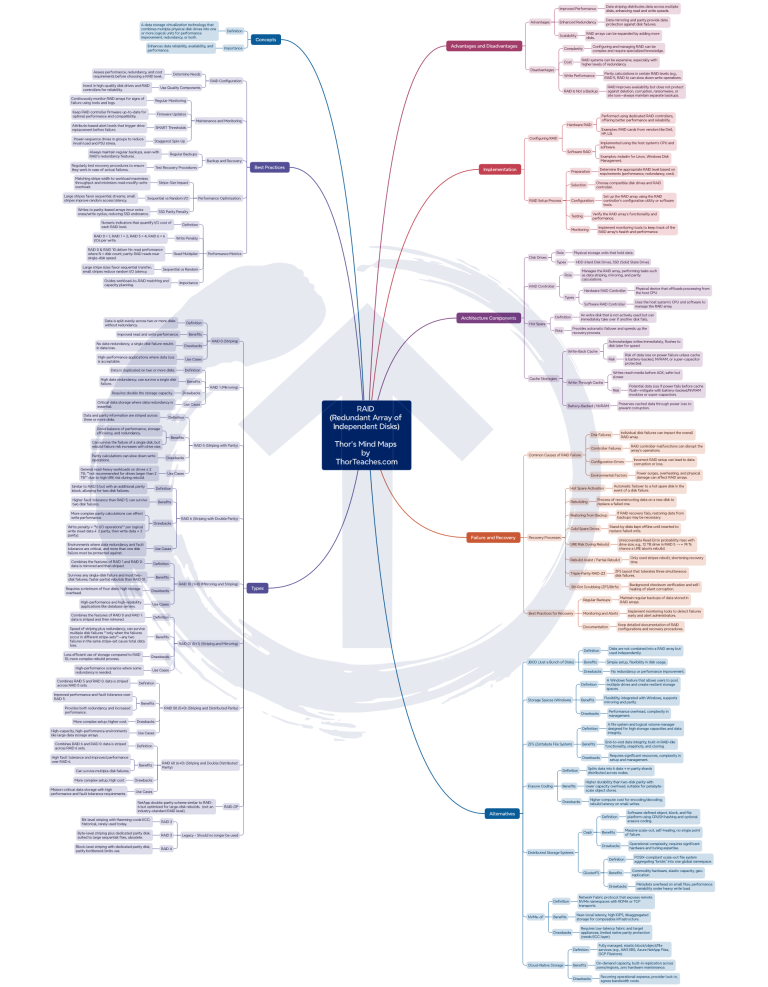
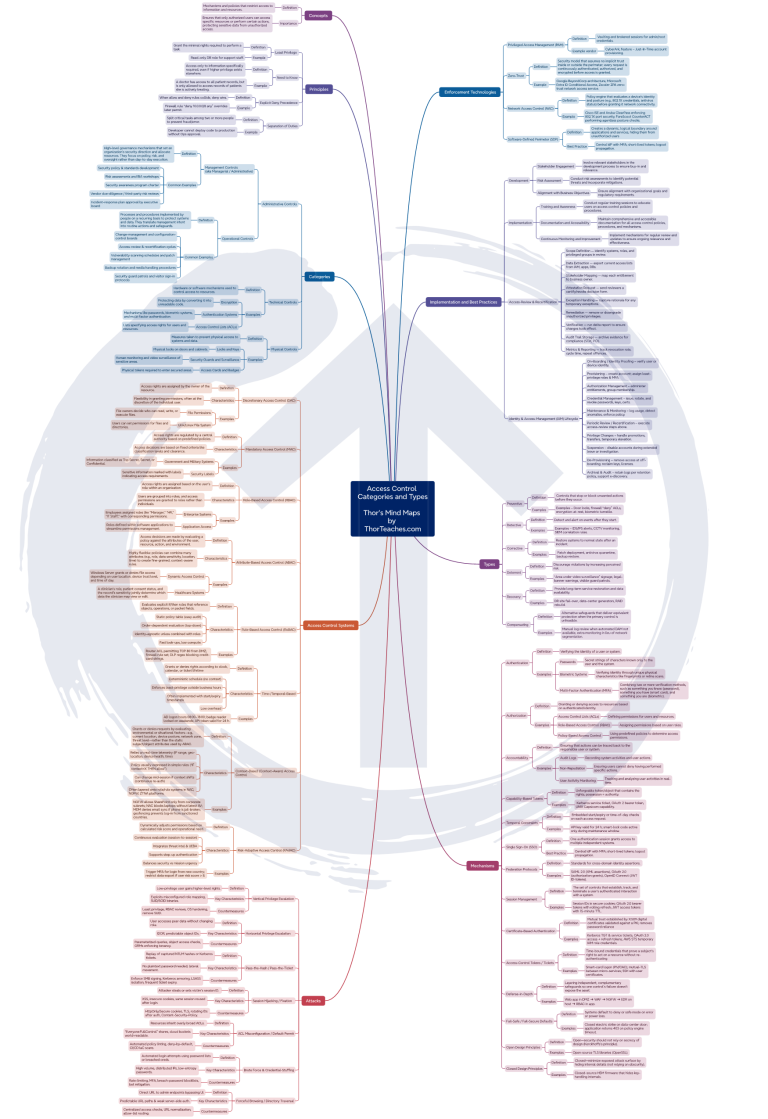
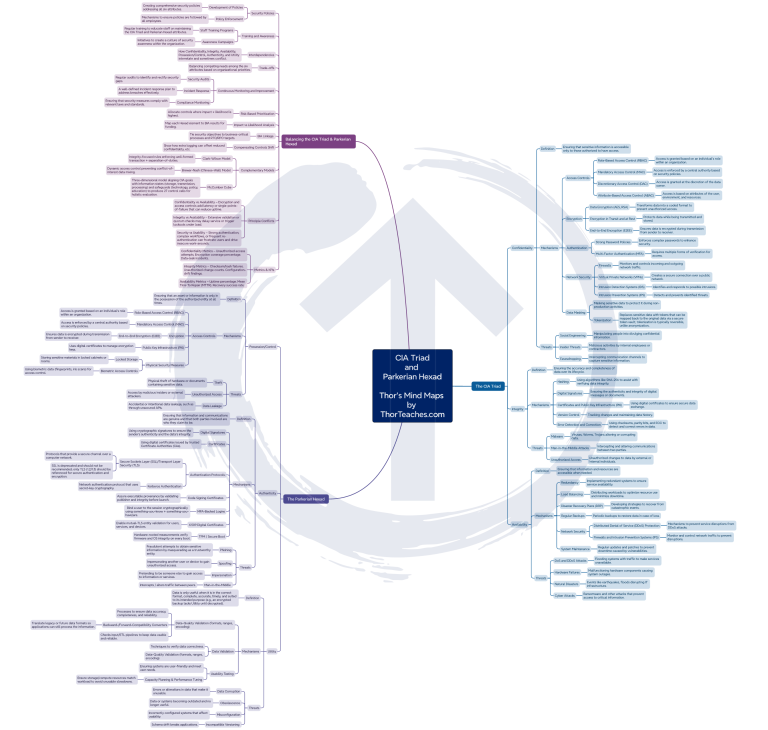
34 CISSP Mind Maps
-
2,800 Upgraded CISSP Flashcards From anywhere, on any device, at any time (web, Android, iOS apps).
Automated reminders, progress tracking, optimized spaced repetitions, confidence-based algorithm. -
A 300-page PDF CISSP study guide 120-page PDF Quick Sheets
PDF Mnemonics
A CISSP Study Plan -
The 24/7 CISSP ThorBot (chatbot)
-
A 2,500 word CISSP glossary
-
Subtitles English, Spanish (Latin America), Portuguese (Brazil),
French, Arabic, Chinese, Japanese, and Hindi -
Lifetime or 12-months access
-
Updated in 2025
12-months access $329.95
I will pass the exam in less than 1 year.
Lifetime Access $449.95
Lifetime Access please, you just never know.
4-minute video overview of all the materials
You will learn the 4 things you need to pass your CISSP exam!
- The knowledge: So you can explain the where/when/why/how/what of any topic.
- Question deconstruction: To figure out; what are they ACTUALLY asking here?
- Answer logic: The ability to pick the MOST right answer in the eyes of ISC2, there may be 2 more or less right answers.
- Time management: You have at least 72 seconds per exam question, assuming 150 questions.
Preview some of our Complete CISSP Bundle materials:
-
34 hours of CISSP videos
-
5,000+ CISSP questions 625 Hard CISSP questions
750 Complex questions
3,250 Easy/Mid questions
- Both Exam emulation tests and Per-Domain tests
201 After Topic questions
240 After Domain questions
Try 25 of our CISSP practice questions:
You get detailed explanations for ALL the questions!
Please wait...![]()
-
2,800 Upgraded CISSP Flashcards
Why these work better:
🧠 Spaced-repetition algorithm → Focus on weak spots, skip strengths
⚡ Quick study sessions → 5-minute bursts or longer sessions
🌍 Study anywhere, even offline → Web, iOS, Android stay in sync
🔍 Two explanation levels for every term → Brief answers plus detailed explanations
What you get:
🎓 Complete deck → 2,800+ flashcards for all 8 CISSP domains
🔗 Learning links → Links to CISSP lectures and Wikipedia for deeper learning
📊 Progress tracking → Study reminders and motivation tools
📲 Cross-platform sync → Web, iOS, and Android apps
-
The 24/7 CISSP ThorBot (chatbot)
Try the ThorBot (Light):
You get the Full version with the course bundles.
The Light version is only trained on Domain 1 materials.
Type above here to try the ThorBot (Light)
ThorBot is using ChatGPT-4o
(We update to the latest model when they are released).
The ThorBot has been trained on:
- All our Curriculum videos
- All relevant NIST documents
- 500+ relevant Wikipedia pages
- The Official ISC2 and ISACA websites
- Our "How to study" course
- OWASP top 10
- The Memory Palace study guide
- The Sunflower notes study guide
- The CISSP Process Guide
- Our own Study guides and more ...
-
34 CISSP Mind Maps
Detailed Mind Maps for all 8 domains, covering all major topics



-
A 2,500 word CISSP glossary
Try our CISSP Glossary!
12-months access $329.95
I will pass the exam in less than 1 year.
Lifetime Access $449.95
Lifetime Access please, you just never know.
Don't need the videos? Get ONLY the Questions:
Reminder: These courses ONLY have the questions.
They do NOT have the curriculum videos, Mind Maps, the study guides,
the 2,800 flashcards, the ThorBot chatbot, or the 2,500 word glossary.
Easy/Mid/Hard Question ONLY
- 4,625 questions:
- 625 Hard questions
- 750 Complex questions
-
3,250 Easy/Mid questions
both as exam emulation and domain tests. - Lifetime or 12-months unlimited access
- (Optional +$75) 700 Boson Hard questions.
- Updated for the 2024 curriculum
12-months access $224.95
I will definitely finish studying in less than 1 year.
Lifetime Access $299.95
Lifetime Access please, you just never know.
Hard Questions ONLY
- 625 Hard questions
- 750 Complex questions
- Lifetime or 12-months unlimited access
- (Optional +$75) 700 Boson practice questions.
- Updated for the 2024 curriculum
12-months access $119.95
I will definitely finish studying in less than 1 year.
Lifetime Access $159.95
Lifetime Access please, you just never know.
Frequently asked CISSP questions:
How should I study for the CISSP exam?
This is the approach I use for all my own studying and it seems to work for the majority of my students.
I cover it all in my Free CISSP study course, get it here! >>
Find your CISSP study materials, get 1-3 good video courses, 1-2 good books, and do 3,000 – 5,000 practice questions before the exam.
- Watch each video class once without/with taking notes.
- Read the primary book once, read everything, and highlight what you think is important or what the book tells you is important. Add to your notes.
- (Do some per domain practice tests, restudy EVERYTHING you get wrong/are unclear on).
- (Re-watch each video class, and add to your notes).
- (Re-read the primary book /and or) read the secondary book if you have it, read everything, and highlight what you know is important. Add to your notes.
- Read the free study guides and supplement your notes.
- Start on per-domain practice tests, start with easy/mid practice questions. Do a test then restudy EVERYTHING you get wrong/are unclear on. Do this for 2,000-3,000 questions or you consistently hit 80%+ on easy/mid questions. Add to notes as appropriate.
- ̉Switch to Hard/Complex questions, same process as easy/mid. Take a test, then restudy EVERYTHING you get wrong/are unclear on. It is perfectly normal to score 50-60% on your first Hard/Complex tests, it is normal and OK. The whole idea of Hard/Complex questions is to get you ready for complex scenarios and deconstructing questions. Spend more time deconstructing questions with Hard/Complex questions.
Books, videos, study guides, google, GenAI, and study groups are for gaining knowledge.
Easy/mid questions are for finding the large knowledge gaps.
Hard/Complex questions are for getting the right mindset and learning to logic your way through complex scenarios and deconstructing questions.
You will need all 3 categories to gain a higher chance of passing your exam.
The CISSP exam question pool is supposedly over 10,000 questions large and growing. This means that no practice test engine will ever “be like the exam” and brain-dumps will NOT work.
You need to understand ALL the concepts, be able to explain them and be able to logic your way through complex convoluted exam questions.
Most students score 80-85% on easy/mid practice questions, then move to Hard/Complex questions and score 50-60%, remember, this is normal and OK. I have many students who do not score over 60-65% on my Hard/Complex questions and pass the exam.
Use easy/mid questions early in your studying and Hard/Complex questions the last 1-2 months.
You need to spend a good deal of time learning to deconstruct questions; what are they really asking here?
Do not worry if you spend 3-5 minutes on a question to begin with; just learn to deconstruct the question.
Deconstruct questions and answers:
- Read the question; spot the keywords (PKI, Integrity, HIPAA) and indicators (FIRST, MOST, BEST), then deconstruct the question; what are they really asking here?
- Once you have deconstructed the question, read the answer options.
- Deconstruct the answer options too, if needed.
Many questions have 2 distractors and 2 possible right answers.
In rare cases, there can also be 4 wrong answers (you then pick the LEAST wrong answer) or 4 right answers (you then pick the MOST right answer).
Do not use the same practice questions more than once. You will get higher scores, but it will be inaccurate scores; you have seen the questions before.
After each practice test, review all the questions you got wrong and the ones you marked for review, and read the question explanation. Then re-read the book and, re-watch the video, use Google on the topics you answered wrong on the test.
Re-study the topic until you understand WHY the right answer is the right answer, and why you answered it wrong.
This is critical; you need to grow your knowledge, not just grind out practice tests.
For the last 2-4 weeks, do Hard/Complex questions, use the free study guides, read the 11th hour, and re-watch all the videos at 1.5x – 2x speed; this is just to refresh the topics you covered earlier in your studying.
I normally do not recommend studying on exam day, but it can be beneficial to do 5-10 questions right before the test to get in the right mindset just prior to the exam (read in the parking lot or similar).
What's the job outlook like for CISSP professionals?
I can’t promise you anything, but there is a huge demand for Certified Information Systems Security Professional (CISSP) certified professionals, there are currently over 74,228 open CISSP jobs in the US alone and we are seeing the same picture across the world.
The average CISSP salary in the US is over $147,757 per year, worldwide that number is $119,571. CISSPs on average make 35% more than their non-certified colleagues.
Can I preview your CISSP study materials before I buy?
Yes, you can see examples of the videos, study guides, mnemonics, practice questions, glossary, flashcards, and the ThorBot (Chatbot) below.
What changed in the 2024 CISSP exam update?
The short version:
The Exam changes are minor, maybe 2-4% total.
The CISSP 2024 exam update, includes a 1% weight shift from Domain 8 to Domain 1, fewer exam questions (100 to 150 instead of 125 to 175), and a shorter exam duration (3 hours instead of 4). Additionally, there’s an update in curriculum content across various domains, including new and expanded topics.
My video on the CISSP 2024 exam changes:
The longer version:
What are the actual curriculum changes?
Most of the changes is more emphasis on topics that are more relevant and in focus now like cloud computing, AI, privacy, etc.
Domain 1: Added external dependencies in business impact analysis.
Domain 2: No changes we know of.
Domain 3: Added Secure Access Service Edge (SASE), Quantum key distribution, and managing the information system lifecycle.
Domain 4: Added transport architecture, performance metrics, traffic flows, physical segmentations, edge networks, virtual private clouds, and network monitoring and management.
Domain 5: Added services in the control of physical and logical access to assets, policy decision and enforcement points, and service account management.
Domain 6: Emphasis on location context (on-premise, cloud, hybrid) for audit strategies.
Domain 7: Added communication during the testing of Disaster Recovery Plans (DRP).
Domain 8: Added Scaled Agile Framework and software composition analysis.
Are your courses updated for the 2024 CISSP changes?
Yes, completely.
When new exams come out do I need to buy your courses again?
No, we always do in-place upgrades, meaning if you have access you always get our updates for free on ThorTeaches.com and Udemy.
Can I take the CISSP exam remotely?
No, all exams must be taken in-person at an authorized Pearson-Vue testing center.
Can I use materials from the old exam version?
You should be fine, the changes are very minor. It is advisable to review the new topics from other sources as the update will introduce new content.
Did the format of exam change in the updated CISSP exam?
No, the format will remain Computer Adaptive Testing (CAT), but there will be a total of 100 to 150 questions instead of the previous range of 125 to 175.
How much time will I have per question in the updated exam?
If you receive the maximum of 150 questions in your exam, you will have approximately 72 seconds per question within the 3-hour time limit.
What is the passing score for the updated CISSP exam?
The passing score for the CISSP exam remains the same, which is a scaled score of 700 out of 1000 points.
Are beta questions be included in the updated CISSP exam?
Yes, there are be 25 beta questions randomly dispersed within the first 100 questions of the exam.
Are the beta questions counted towards the final score?
No, beta questions are not counted toward your final score. They are used by ISC2 to validate the questions for future exams.
Are the beta questions be distinguishable from the scored questions?
No, you will not be able to distinguish beta questions from scored questions during the exam.
Are there new types of interactive questions in the updated CISSP exam?
There is no specific mention of new question types; the update focuses on content rather than question format.
How did the changes affect the weight of each domain in the CISSP exam?
All domains except for Domain 1 and Domain 8 will maintain their previous weights. Domain 1 increased by 1%, compensated for by a 1% decrease in Domain 8.
How often are the CISSP exam and the exam questions updated?
The exam updates every 3 years, the actual exam questions are updated continually.
What is included in your courses?
All this is included in our courses:
- 34 hours of CISSP videos (over 200 lectures covering all 8 CISSP domains).
- 5,000+ CISSP practice questions.
- 625 hard CISSP practice questions, in 5 tests.
- 750 Complex practice questions, in 6 tests.
- 3,250 Easy/Mid CISSP questions – both as exam emulation (26 tests) and domain tests (32 tests).
- 201 topic questions after each major topic.
- 240 domain questions, 30 after each domain.
- CISSP Study Guides – 300+ pages.
- 2,800 Upgraded CISSP Flashcards
- Access from anywhere, on any device, at any time (web, Android, iOS apps).
- Automated reminders, progress tracking, optimized spaced repetitions, confidence-based
- A 2,500 word Glossary
- CISSP Quick Sheets – 120 pages (for review sessions).
- ThorBot: Your 24/7 AI study assistant, clarify concepts, tailor your learning, and enhance your CISSP preparation.
- A CISSP study plan.
- 450+ CISSP links.
- CISSP Mnemonics.
- Subtitles in English, Spanish (Latin America), Portuguese (Brazil), French, Arabic, Chinese, Japanese and Hindi
- (optional) 700 Boson practice questions.
- 2024 curriculum updated.
Can I rewatch the videos and do the practice questions more than once?
Yes!
You have access to our courses for either Lifetime or 12 months, you can watch the videos and do the practice questions as many times as you want.
What do I need to know about the CAT exam format?
The CISSP CAT (Computerized Adaptive Testing) exam format uses an adaptive algorithm that tailors questions to the test taker.
You will get between 100 and 150 questions, and you have 3 hours to finish the test, that is 72 seconds per question (assuming 150 questions) which should be plenty, but still, keep an eye on the clock.
If you go above 100 questions do not panic, you still have a good chance of passing, the exam will keep giving you questions until it predicts with 95% probability that you will pass or fail or when you hit question 150.
25 of the first 100 questions are beta questions, they do not count, you do not know which they are. and it is not the first 25, it is random. They are used by ISC2 to test possible future exam questions.
You need to score proficient (around 70%) in all 8 CISSP domains to pass the exam, if you are below in certain domains the exam will keep giving you questions from those domains until you pass or fail.
What are the prerequisites for earning my CISSP certification?
To get your Certified Information Systems Security Professional (CISSP) certification you must have at least 5 years of professional experience in the information security field.
Your work experience must fall within two or more of the eight domains of the ISC2 CISSP CBK:
Domain 1. Security and Risk Management
Domain 2. Asset Security
Domain 3. Security Architecture and Engineering
Domain 4. Communication and Network Security
Domain 5. Identity and Access Management (IAM)
Domain 6. Security Assessment and Testing
Domain 7. Security Operations
Domain 8. Software Development Security
You may satisfy one year of required experience by holding one of the following below (you will then need four years of relevant work experience):
Four-Year College Degree or Regional Equivalent or Approved certification on the ISC2 Approved List
https://www.isc2.org/Certifications/CISSP/experience-requirements
What are the exam domains?
There are 8 domains in the ISC2 CISSP Common Body of Knowledge (CBK) 2024.
Domain 1: Security and Risk Management – making up 16% of the weighted exam questions.
Domain 2: Asset Security – making up 10% of the weighted exam questions.
Domain 3: Security Architecture and Engineering – making up 13% of the weighted exam questions.
Domain 4: Communication and Network Security – making up 13% of the weighted exam questions.
Domain 5: Identity and Access Management (IAM) – making up 13% of the weighted exam questions.
Domain 6: Security Assessment and Testing – making up 12% of the weighted exam questions.
Domain 7: Security Operations – making up 13% of the weighted exam questions.
Domain 8: Software Development Security – making up 10% of the weighted exam questions.
What are the renewal requirements?
CISSP certification holders are required to earn 120 CPEs per 3-year cycle, pay a $135 Annual Maintenance Fee (AMF) and adhere to ISC2’s Code of Ethics.
ISC2 CPE FAQ:
https://www.isc2.org/Insights/2024/05/Managing-Your-ISC2-CPE-Credits-and-Activities
ISC2 CPE YouTube videos on how to submit CPEs:
https://www.youtube.com/playlist?list=PLZEQg62IaANAJwZQGat-AjihyrYmS8wEq
You can add CPEs here: https://cpe.isc2.org/s/









