RBAC (Role Based Access Control): Often used when data integrity is most important.
Most large organizations use role based access control, your access levels are determined by your job role.
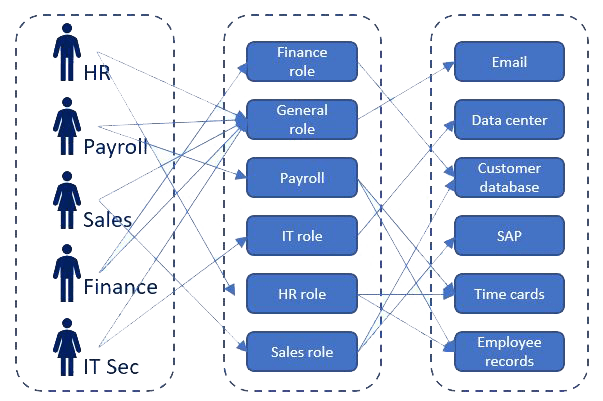
- Policy neutral access control mechanism defined around roles and privileges.
- A role is assigned permissions, and subjects in that role are added to the group, if they move to another position they are moved to the permissions group for that position.
- It makes administration of 1,000’s of users and 10,000’s of permissions much easier to manage.
- The most commonly used form of access control.
- If implemented right it can also enforce separation of duties and prevent authorization/privilege creep .
- We move employees transferring within the organization from one role to another and we do not just add the new role to the old one.

